Preventing terrorists and violent extremists from exploiting digital platforms
Preventing terrorists and violent extremists from exploiting digital platforms
The Global Internet Forum to Counter Terrorism brings together the technology industry, government, civil society, and academia to foster collaboration and information-sharing to counter terrorist and violent extremist activity online.
GIFCT’s strategic planning and programming centers on three pillars:
Prevent
PreventDelivering critical information and the capacity to prevent and disrupt terrorist and violent extremist activity online |
Respond
RespondCoordinating and continually strengthening the tech ecosystem’s response to the online impacts of terrorist or violent extremist incidents |
Adapt
AdaptConvening industry, experts, and civil society to understand emerging trends relating to technology, terrorism, and violent extremism |
Research and Resources from our Core Partners

Global Network on Extremism & Technology
Recent insights, reports, and digests from our academic research arm
- Apr 23 2024
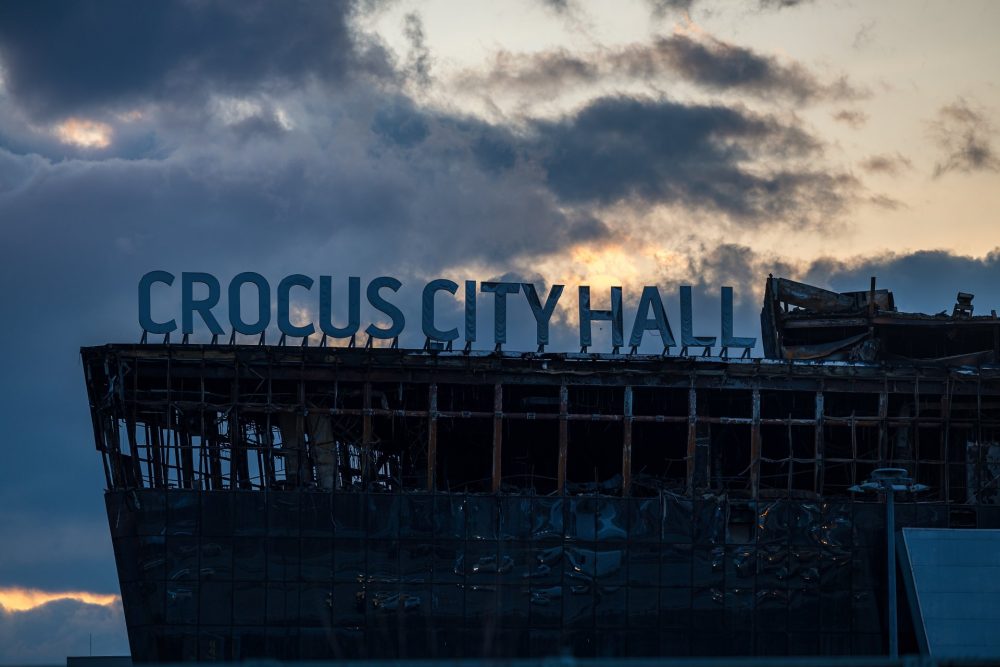
Moscow Attack: The Popularisation of Far-Right Conspiracy Theories in Mainstream Media
Introduction In the immediate aftermath of the 22 March attack on Moscow’s Crocus City Hall,...Read more - Apr 17 2024

The Radicalisation of Digital Playgrounds: The Need for Multistakeholder Dialogue
Introduction The potential nexus between gaming and radicalisation into extremism has become a hot topic...Read more - Apr 15 2024

Unveiling Terrorist Influence: The Case of Pakistan’s 2024 General Elections
Introduction Elections in fragile democracies are often the targets of terrorist exploitation. Notably, general elections...Read more - Apr 10 2024

Eyes in the Sky: The Innovation Dilemma of Drone Proliferation among Violent Non-State Actors in the Sahel
Introduction The Sahel, with its vast geographical expanse and porous borders, has become a hub...Read more
Tech against Terrorism
Latest news from our mentorship and knowledge-sharing partner here
X Feed
Last month, GIFCT worked with @BSRnews to convene an expert discussion on practical #humanrights-based approaches to preventing terrorists & ...violent extremists from exploiting digital platforms with @UN_OCT & @article19UN.
Here's a summary of the panel:
https://gifct.org/2024/04/22/human-rights-based-approaches/
GIFCT had the pleasure of hosting with @firjan a Latin America regional workshop in Rio yesterday, bringing together participants from tech, industry... bodies, local CTVE experts, and UN & government representatives to explore the intersections of #technology and #counterterrorism.
"Having a space to collaborate with other platforms is extremely beneficial to us and our industry as a whole. This is something GIFCT provides... a ...place where we can share technical tools, but also... knowledge... " said Lucas Gagliardi of @yubo_app, a GIFCT member company.
A big thanks to all our participants and supporters for their valuable contributions. This is GIFCT's 18th Regional Workshop since its inception.
...For more information about our programming, please visit http://www.gifct.org.
A reminder that the deadline to apply for the position of Director of Technology Policy & Solutions is this Friday, April 19th!
#hiring ...#HiringNow #TechJob
GIFCT is looking for a collaborative & diligent worker who possesses a demonstrated interest in online platforms, terrorism & violent ...extremism, and public policy to support its programming activities as a Spring Fellow.
Monday is the deadline!
Apply →
The threat landscape & implications for terrorism & violent extremism online are always evolving. So is GIFCT.
We're working w/ our members ...& partners towards a world in which the tech sector renders terrorists & violent extremists ineffective online.
→ https://bit.ly/2023GIFCT
